Users
We estimate the number of users by analyzing the requests induced by clients to relays and bridges.
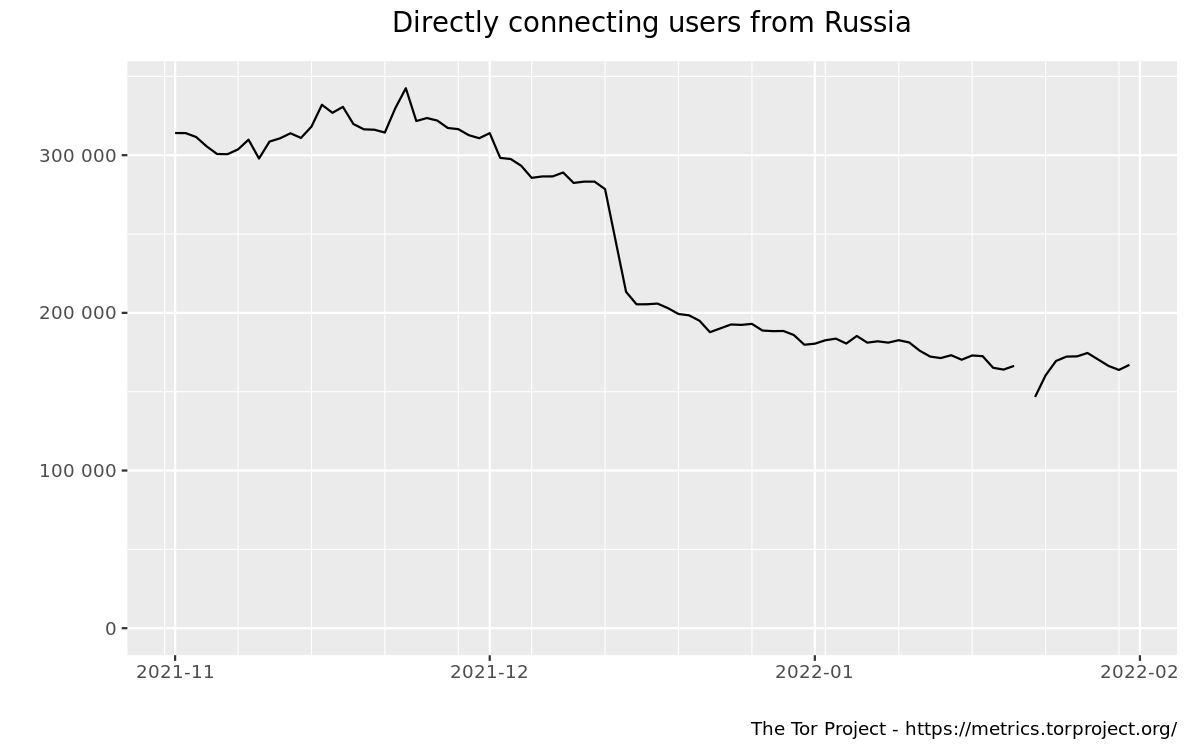
This graph shows the estimated number of directly-connecting clients; that is, it excludes clients connecting via bridges. These estimates are derived from the number of directory requests counted on directory authorities and mirrors. Relays resolve client IP addresses to country codes, so that graphs are available for most countries. Furthermore, it is possible to display indications of censorship events as obtained from an anomaly-based censorship-detection system (for more details, see this technical report). For further details check the documentation on Reproducible Metrics.
Related events
The following events have been manually collected in the metrics-timeline Git repository and might be related to the displayed graph.
| Dates | Places/Protocols | Description and Links |
|---|---|---|
| 2022-01-31 | snowflake |
Switched the snowflake bridge from a load-balanced staging server back to the now load-balanced production server. Debugged connection problems until 2022-01-31 19:52:04.
issue comment comment |
| 2022-01-28 | snowflake |
Switched the snowflake-server (at the time running on a load-balanced staging server) for a version with CPU profiling.
comment |
| 2022-01-25 | snowflake |
Switched the snowflake bridge to a temporary load-balanced staging server. Debugged connection problems until 2022-01-25 18:47:00.
issue comment post comment |
| 2022-01-07 | snowflake |
Increased capacity of the mapping to client IP addresses on the snowflake bridge.
issue deployment comment |
| 2021-12-29 | snowflake |
Outage of the snowflake bridge.
comment alert |
| 2021-12-24 | Russia obfs4 |
Another round of obfs4 enumeration and blocking occurs in Russia.
comment |
| 2021-12-22 | snowflake |
Rebooted the Snowflake bridge to increase the number of CPUs from 4 to 8.
issue |
| 2021-12-14 | snowflake |
Release of Tor Browser 11.5a1, with an altered DTLS fingerprint in Snowflake to counteract blocking in Russia.
blog post issue NTC post |
| 2021-12-13 | Russia |
The fraction of networks in Russia blocking Tor, measured by OONI, increases from about 20% to about 50%.
relay graph |
| 2021-12-08 | obfs4 |
Release of Tor Browser 11.0.2, containing a new default obfs4 bridge "deusexmachina".
blog post issue |
| 2021-12-08 | Russia |
The Tor Project web server block is expanded from *.www.torproject.org to *.torproject.org.
record GitLab comment NTC comment zapret-info diff |
| 2021-12-07 | Russia |
The www.torproject.org web server is added to the registry of blocked domain names in Russia, by IP addresses and by hostname *.www.torproject.org.
record GitLab comment NTC comment zapret-info diff OONI report |
| 2021-12-01 to 2021-12-13 | Russia meek |
Blocking of the IP address of the meek-azure front domain in certains ISPs in Russia, part of a wider phenomenon of blocking Tor beginning 2021-12-01.
post about start (2021-12-03) post about end (2021-12-13) post about end (2021-12-15) post about end (2021-12-26) |
| 2021-12-01 to present | Russia |
Blocking of Tor directory authorities, relays, default obfs4 bridges, meek-azure, and Snowflake in some ISPs in Russia. There was a temporary cease of blocking for less than a day starting on 2021-12-08.
NTC thread BBS thread issue blog post OONI report |
| 2021-11-17 to 2022-02-02 | obfs4 |
Run a Tor Bridge campaign, offers rewards for running obfs4 bridges.
blog post about start blog post about end |
| 2021-11-08 |
Removal of roughly 600 "KAX17" non-exit relays.
mailing list post relay graph article |
|
| 2021-11-08 | onion |
Release of Tor Browser 11.0. Final deprecation of v2 onion services.
blog post deprecation timeline graph |
