Users
We estimate the number of users by analyzing the requests induced by clients to relays and bridges.
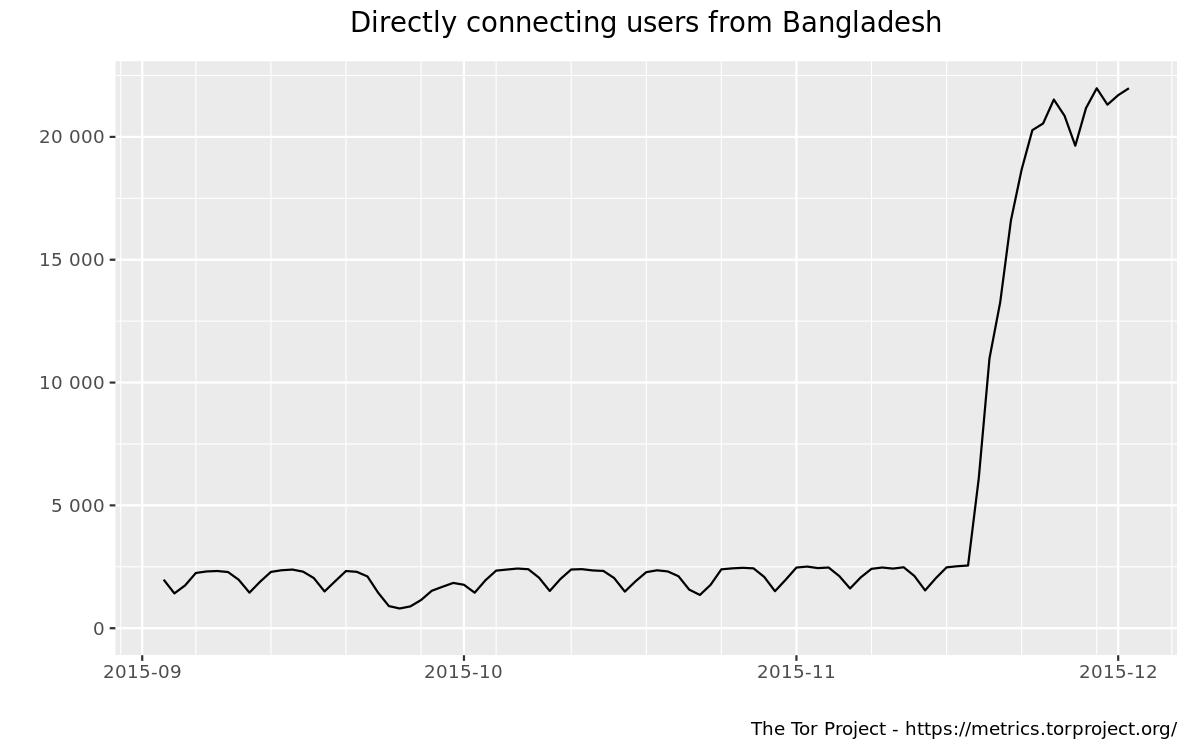
This graph shows the estimated number of directly-connecting clients; that is, it excludes clients connecting via bridges. These estimates are derived from the number of directory requests counted on directory authorities and mirrors. Relays resolve client IP addresses to country codes, so that graphs are available for most countries. Furthermore, it is possible to display indications of censorship events as obtained from an anomaly-based censorship-detection system (for more details, see this technical report). For further details check the documentation on Reproducible Metrics.
Related events
The following events have been manually collected in the metrics-timeline Git repository and might be related to the displayed graph.
| Dates | Places/Protocols | Description and Links |
|---|---|---|
| 2015-11-18 to 2015-12-10 | Bangladesh <OR> obfs3 obfs4 |
Bangladesh blocks Facebook, WhatsApp, and Viber.
news article (archive) relay graph |
| 2015-11-04 | meek |
Tor Browser 5.0.4 and 5.5a4 released, containing a fixed fingerprint for meek-amazon.
5.0.4 blog post 5.5a4 blog post ticket |
| 2015-10-30 | meek |
Altered the performance settings on the meek-google App Engine instance. Set max idle instances to 2 and min pending latency to 1000 ms. This used to be configured through the web interface but is now configured in an application file, which at some point caused the settings from 2015-02-28 to be lost.
|
| 2015-10-30 | meek |
Further rate-limited the meek-azure bridge to 0.8 MB/s, from 1.1 MB/s.
|
| 2015-10-09 | ipv4 ipv6 |
geoip and geoip6 databases updated to "October 9 2015 Maxmind GeoLite2 Country" (geoip-db-digest 5BF366AD4A0572D82A1A0F6628AF8EF7725E3AB9, geoip6-db-digest 212DE17D5A368DCAFA19B95F168BFFA101145A93).
commit |
| 2015-10-09 | meek |
The fingerprint of the meek-amazon bridge changes, as a result of begin rebooted. Released Tor Browsers with the former fingerprint are unable to connect. The fingerprint changed from 4EE0CC769EB4B15A872F742EDE27D298A59DCADE to 6DDD1DB8526282837C50E9AB5D14AB50150CD624, then again to B9E7141C594AF25699E0079C1F0146F409495296. The new fingerprint shipped with Tor Browser 5.0.4 and 5.5a4 on 2015-11-04.
ticket |
| 2015-10-02 | meek |
Rate-limited the meek-azure bridge to 1.1 MB/s. (Azure grant expired.)
|
| 2015-09-30 to 2015-10-09 | meek |
Outage of meek-amazon caused by an expired certificate. As a result of being rebooted, the bridge also changes its fingerprint from 4EE0CC769EB4B15A872F742EDE27D298A59DCADE to 6DDD1DB8526282837C50E9AB5D14AB50150CD624.
mailing list post about start mailing list post about end ticket |
| 2015-09-24 | ipv4 ipv6 |
geoip and geoip6 databases updated to "September 3 2015 Maxmind GeoLite2 Country" (geoip-db-digest 022B9BADD23D743E51F165FB4C87E78E59F0BCB8, geoip6-db-digest DE13219FCF0F27999D1F91174CF80291B1746C95).
commit |
| 2015-09-23 | meek |
Upgraded meek-azure bridge from KVM to Xen.
blog post |
