Users
We estimate the number of users by analyzing the requests induced by clients to relays and bridges.
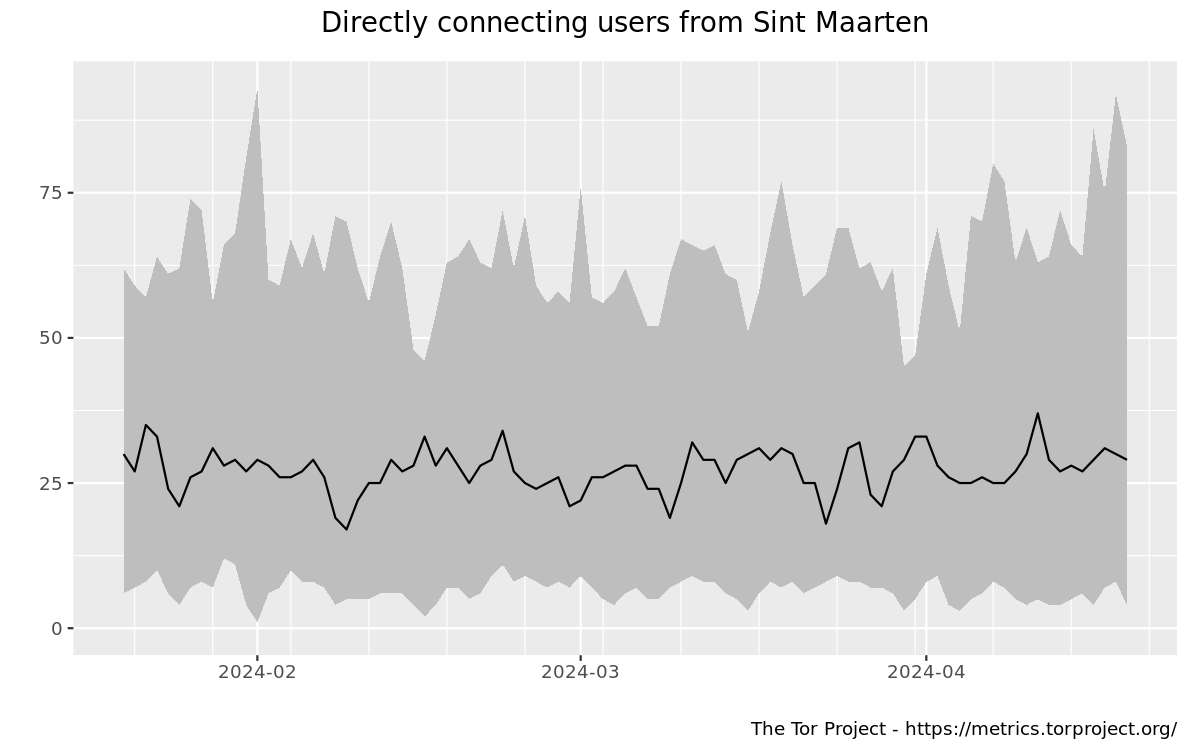
This graph shows the estimated number of directly-connecting clients; that is, it excludes clients connecting via bridges. These estimates are derived from the number of directory requests counted on directory authorities and mirrors. Relays resolve client IP addresses to country codes, so that graphs are available for most countries. Furthermore, it is possible to display indications of censorship events as obtained from an anomaly-based censorship-detection system (for more details, see this technical report). For further details check the documentation on Reproducible Metrics.
Related events
The following events have been manually collected in the metrics-timeline Git repository and might be related to the displayed graph.
The manually collected events in this table do not necessarily match the automatically generated possible censorship events shown in the graph.
| Dates | Places/Protocols | Description and Links |
|---|---|---|
| No events are known that might be related to the displayed graph. | ||
